OSI Model #
The OSI model frequently confuses engineers and is often dismissed as a faded, abstract concept. In reality, it is the fundamental core of computer networking. Without it, a Backend or DevOps engineer simply cannot unlock their full potential. Terms like segments, packets, frames, and L4 vs. L7 load balancing dominate IT conversations, yet few truly grasp them. I previously set the stage for these concepts in my HTTPS and SSL article. This article bridges the remaining gaps by mastering the foundational layers.
I will try to explain it in the simplest way, using just a diagram.
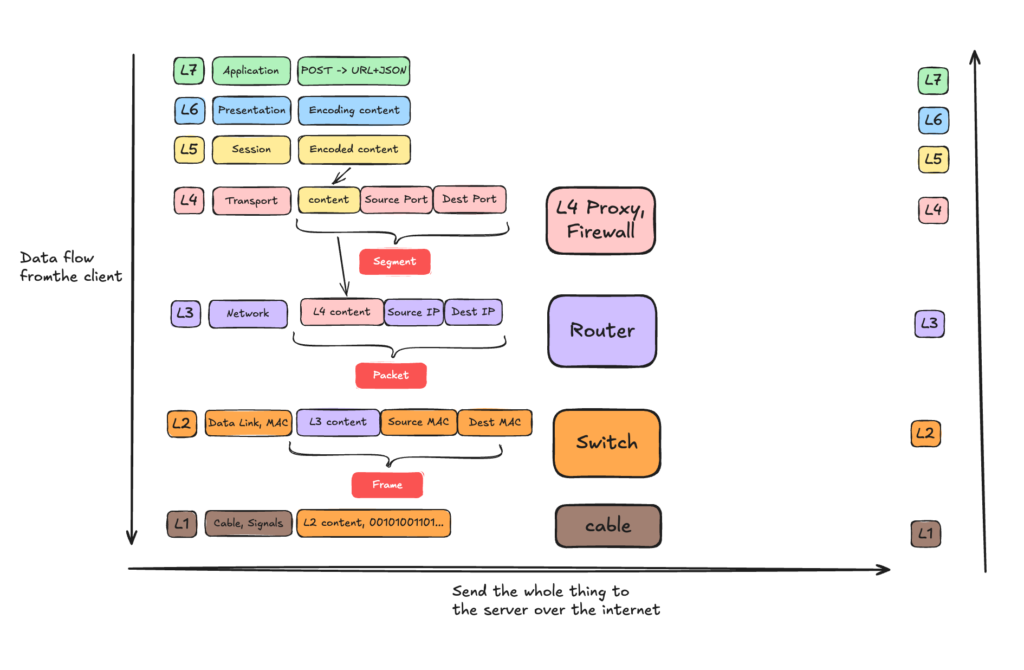
This diagram illustrates the data flow from a client application down through each OSI layer. As the data descends, you can see exactly how it is enriched at each stage—turning into Segments at L4, Packets at L3, and Frames at L2. The diagram also maps the specific network hardware (Proxies, Routers, and Switches) that handle these data units. Finally, the data travels across the physical medium (L1) and ascends the server’s network stack from Layer 1 up to the Layer 7 application to process the incoming POST request.
IP for Dummies #
CIDR Notation & Subnetting #
In networking, you will usually see IP addresses formatted like this: a.b.c.d/x. This is known as CIDR notation, and it is used to define the IP range of a subnet.
The /x shows you exactly how many bits are locked down for the network, and how many bits remain free for the hosts (devices) on that network.
Let’s say we have 192.168.1.0/24. An IPv4 address consists of 4 blocks (octets), and each block is exactly 8 bits, totaling 32 bits.
In binary, 192.168.1.0 looks like this:
11000000 . 10101000 . 00000001 . 00000000
The /24 means that the first 24 bits are frozen. They belong to the network and cannot change:
First 24 bits (FROZEN) | Remaining 8 bits (FREE)
11000000 . 10101000 . 00000001 | 00000000
[------- 192.168.1 -------] | [-- 0 --]Since the 24 bits are frozen, 32 – 24 = 8 so the total available hosts are 2^8 – 2 = 254.
Network ID: 192.168.1.0 – It represents the network and cannot be assigned to a host.
Broadcast Address: 192.168.1.255 – Data sent here goes to everyone in the network and no host can be assigned to it.
Network Mask: Defines the size of the subnet, often shown as 255.255.255.0 or /24. It is also used to determine if an IP is in the same subnet.
So 192.168.1.1 is the first usable host and 192.168.1.254 is the last usable host.
Use mask to determine if 2 IPs belong to the same subnet #
To find out if two IP addresses are in the same network, a computer performs a fast, elegant mathematical operation called a Bitwise AND.
Lets find out if IP: 192.168.1.5 and IP: 192.168.1.50 are in the same subnet.
IP 1 (Binary): 11000000 . 10101000 . 00000001 . 00000101 (192.168.1.5)
Mask (Binary): 11111111 . 11111111 . 11111111 . 00000000 (255.255.255.0)
----------------------------------------------------------- [Bitwise AND]
Network ID: 11000000 . 10101000 . 00000001 . 00000000 (192.168.1.0)IP 2 (Binary): 11000000 . 10101000 . 00000001 . 00110010 (192.168.1.50)
Mask (Binary): 11111111 . 11111111 . 11111111 . 00000000 (255.255.255.0)
----------------------------------------------------------- [Bitwise AND]
Network ID: 11000000 . 10101000 . 00000001 . 00000000 (192.168.1.0)Both of the IP have the same network ID, so they belong to the same network, so same subnet.
Network Diagnostics (ICMP, Ping, and Traceroute) #
When things break at Layer 3, you need tools to figure out where the connection is dropping.
ICMP (Internet Control Message Protocol) is a helper protocol for the Internet Protocol (IP).
Unlike TCP or UDP, ICMP does not carry application payloads like web pages or file downloads. Instead, it is used by network devices to send error messages and operational information.
TTL: Despite its name, TTL is not measured in seconds or milliseconds. Instead, it is a hop counter that acts as a self-destruct timer for your network packet Every single time your packet passes through a router (a “hop”), that router decreases the TTL value by 1.
Ping: When you run ping 8.8.8.8, your computer wraps an ICMP Echo Request packet inside an IP packet and shoots it across the network. When the destination server receives it, it is obligated to wrap an ICMP Echo Reply packet and send it right back.
Traceroute: While ping tells you if you can reach a server, traceroute shows you the exact path your packet takes to get there. It maps every single router hop along the way. The genius of Traceroute is that it does not use a special protocol. Instead, it intentionally hacks the TTL (Time to Live) rule to force routers to talk to it. It starts with TTL = 1, the next available gateway descrements it to 0 and send back a reply with it’s IP. On the next ping it increments the TTL to 2 and when it reaches the next available gateway after the previous one, the TTL goes also to 0 so now we know the second hop (router) IP.




